Digital Transformation
More Topics
thumbnail
AI & Machine Learning
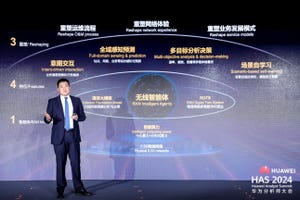
Value from trust: Explainable AI and how to accelerate the automation journey for service providersValue from trust: Explainable AI and how to accelerate the automation journey for service providers
CSPs and their partners are focused on implementing AI in different forms and use cases, and although it is already showing promise in almost every industry, the value from these will come from its deployment at scale. The massive adoption of AI technologies in telecommunications relies on these technologies providing the highest levels of Flexibility, Agility and Trust - characteristics that are central to Explainable AI. Explainable AI (XAI) refers to methods and techniques that produce models which show why and how an AI algorithm has made a certain decision.
Subscribe and receive the latest news from the industry.
Join 62,000+ members. Yes it's completely free.















.jpg?width=300&auto=webp&quality=80&disable=upscale)